A 5-part approach to de-risking AI innovation

Contact center leaders are under intense pressure to adopt AI.
From agent assist and intelligent routing to automation and analytics, AI promises faster service, lower costs and better customer experiences. But layering AI onto a legacy contact center environment is rarely straightforward. These platforms simply weren’t designed with AI in mind. As a result, they often require elaborate custom integrations or significant platform overhauls to bring AI into the fold.
In highly regulated industries, even well‑intended AI integration initiatives can expose legacy contact center stacks to new risks, from data leakage and compliance gaps to reporting errors and operational instability, if the underlying platform limitations and integration requirements are not carefully considered.
Recent research from ShareGate highlights the scale of the problem. In April, nearly one in three organizations reported data exposure incidents linked to AI tools. Personal and personally identifiable information accounted for 30% of the exposed data.
The outcomes of these breaches can be costly. Beyond remediation and legal fees, breaches create reputational damage that is far harder to measure and even harder to undo.
To move forward, organizations need an approach to AI that delivers innovation without compromising the stability and safeguards their legacy contact centers depend on.
Understanding the risk surface AI exposes in modern CX
Modern CX strategies and technologies are designed to capitalize on an interconnected web of integrations spanning data sources, capabilities, and channels. As a result, the modern enterprise risk surface – including organizational assets, data, applications, and more that might be exposed to potential operating risks — has expanded. A disciplined innovation model, therefore, becomes the linchpin between the status quo and the AI-enabled future state.
Applying a defense-in-depth approach to AI adoption safety
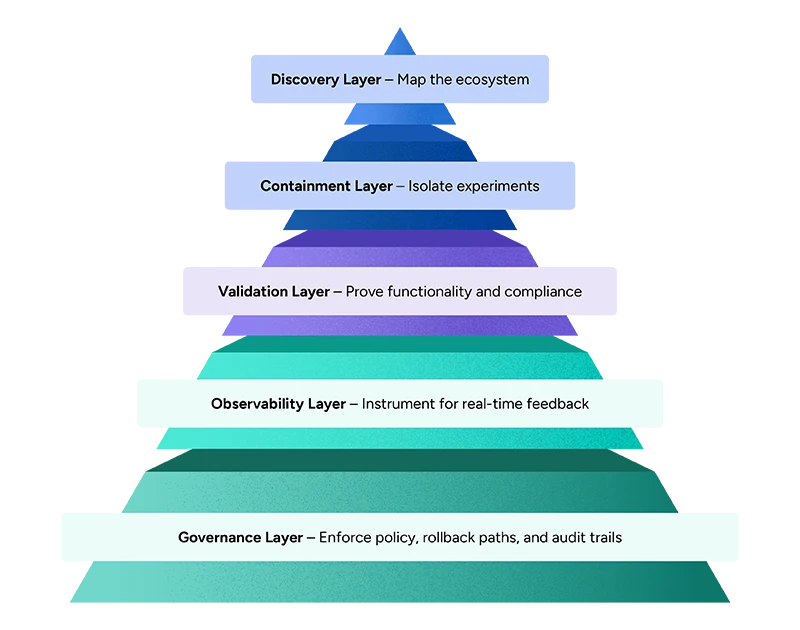
This five-layered safety framework for innovation adoption is modeled on a “defense-in-depth” framework to protect an organization’s technology assets, applications, endpoints, and data both during the transformation process and in the future state. Defense-in-depth deploys multiple layers of security and safeguarding to ensure problems missed by one layer are captured in another layer.
Layer #1: Discovery – Upstream and downstream impact analysis
Effective discovery starts with a full inventory of every system that sends data into, or receives data from, the CX technology stack.
On the downstream side, you must examine reporting and business intelligence warehouses, quality management and workforce optimization suites, customer feedback mechanisms such as post-call surveys, agent training or gamificationportals, and even billing or revenue assurance engines that rely on accuratecall detail records.
Upstream, equal scrutiny belongs to the CRM or case management application that owns interaction metadata, the knowledge management repository whose taxonomy fuels agent assist, the authentication stack that may introduce biometrics or multifactor credentials, the master data layer that synchronizes customer profiles, and the workforce management system whose forecasting models depend on stable queue definitions.
The output of this phase should be three concrete artifacts:
- Current-state and future-state data-flow diagram
- A RACI matrix that clarifies ownership
- A quantified risk register that ranks each dependency by probability and impact
Layer #2: Containment – Safe experimentation patterns
Once the ecosystem is mapped, innovation should be fenced in so that failure is both unlikely and localized. The most common technique is a “feature-toggle” strategy that allows new logic to be activated or deactivated without redeployment. A similar strategy is the canary release, where a small percentage of live traffic — often one to five percent — is routed through the new path while the remainder follows the legacy flow.
Parallel IVRs, sometimes called “shadow” applications, can run in read-only mode to verify intent recognition or menu navigation before they are allowed to control routing. Dual-write data strategies record every transaction in both the old and new schemas until confidence in parity is established. Finally, a cloud “edge” overlay — such as an API gateway — can sit in front of the legacy ACD, enabling modern AI routing or sentiment analysis without disturbing the underlying call-control hardware.
Layer #3: Validation – Testing beyond the happy path
Containment is only useful when paired with rigorous validation. In environments where continuous-integration pipelines are absent, synthetic call generators can flood the system with peak-hour volumes to uncover capacity or codec issues. Contract tests should exercise every API that joins the contact-center core to peripheral platforms, while regression harnesses can replay historical recordings through the new logic to confirm behavioral parity.
Compliance must be verified as well, using purpose-built test suites. Finally, orchestrated fail-over drills — where databases, CRMs, or SSO providers are deliberately taken offline — reveal how gracefully the new solution degrades. Success is measured on two axes: traditional functional KPIs such as average handle time, CSAT, and first-contact resolution, and safety KPIs such as error incidence, data-loss events, and mean time to rollback.
Layer #4: Observability – From logs to business telemetry
Continuous insight requires instrumentation that connects infrastructure events to customer outcomes. Distributed tracing should follow a single interaction from IVR entry through ACD routing into the CRM and agent desktop, delivering end-to-end latency and error visibility.
Real-time anomaly detection models can watch abandonment rates, NPS scores, or IVR containment percentages and raise alerts when they drift outside historical norms. Every record that feeds analytics must carry lineage tags to indicate which version of the data model created it, ensuring analysts know exactly what they are querying.
For deep forensics, a “customer flight recorder” aggregates voice, screen, and metadata so the full journey can be reconstructed after an incident.
Layer #5: Governance – Policies, people, and playbooks
Governance turns one-off heroics into an institutional habit. A cross-functional change-approval board — comprising CX leaders, compliance officers, and security architects — reviews each release for business and regulatory impact. Rollback playbooks define both the technical commands and the business triggers that warrant reversal, eliminating hesitation during an incident. Documentation, configuration files, and even IVR scripts should be version-controlled so that any state of the system can be reproduced on demand.
Agents and supervisors need ongoing training, not only on new features but also on failure scenarios and recovery protocols. Finally, every deployment concludes with a post-implementation review whose lessons feed into the discovery phase, closing the safety loop and ensuring the next innovation cycle starts on firmer ground.
By embedding safety into each layer — discovery, containment, validation, observability, and governance — enterprises can modernize even the most brittle contact-center estates without compromising stability, customer trust or regulatory posture.
[cta-1]
Ready to see what a defense-in-depth approach would look like in your organization?
We can help you assess your risk and identify the right layered adoption strategy to protect your sensitive data.

Larry drives exceptional customer and employee experiences globally, emphasizing CX strategy, operations excellence, and business transformation.


